-
Notifications
You must be signed in to change notification settings - Fork 14
File System Permissions Weakness
Processes may automatically execute specific binaries as part of their functionality or to perform other actions. If the permissions on the file system directory containing a target binary, or permissions on the binary itself, are improperly set, then the target binary may be overwritten with another binary using user-level permissions and executed by the original process. If the original process and thread are running under a higher permissions level, then the replaced binary will also execute under higher-level permissions, which could include SYSTEM.
Adversaries may use this technique to replace legitimate binaries with malicious ones as a means of executing code at a higher permissions level. If the executing process is set to run at a specific time or during a certain event (e.g., system bootup) then this technique can also be used for persistence.
The MITRE page at https://attack.mitre.org/wiki/Technique/T1044 highlights two specific file system permissions weaknesses: service binary replacement and instances of executable installers loading from weakly-ACL'd directories. Veramine's detection engine includes several useful detections rules in these scenarios.
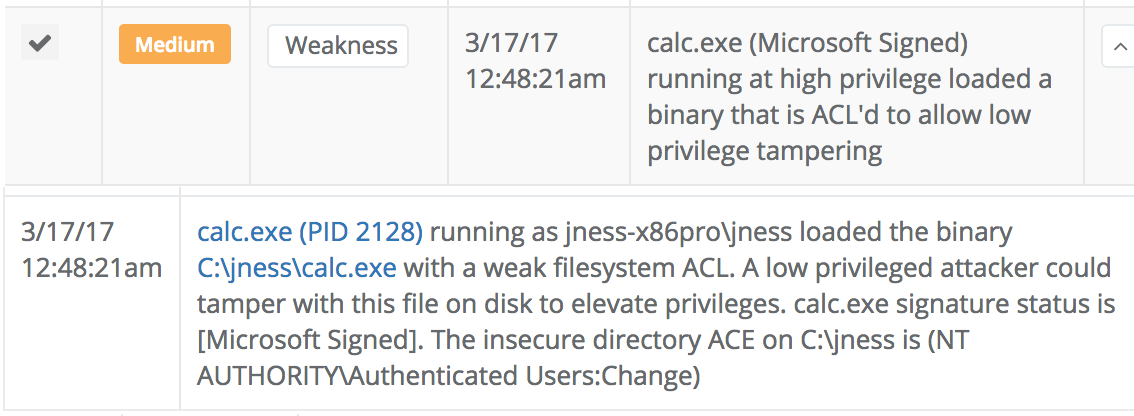
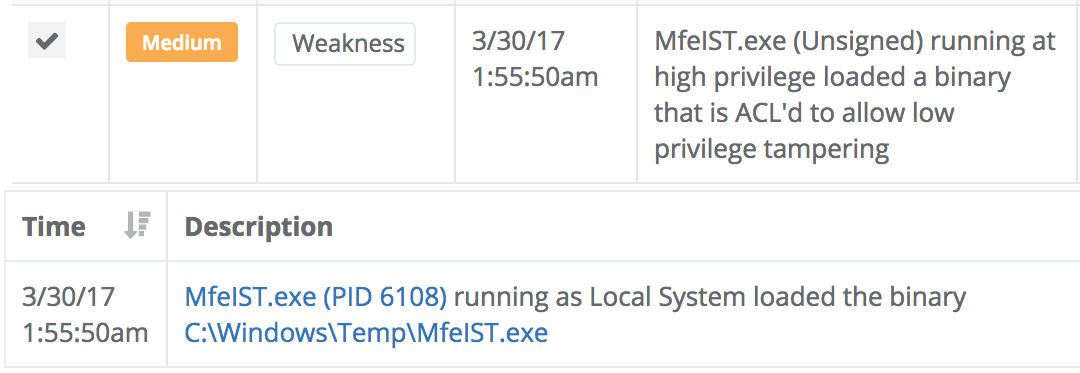
First, the sensor reports every instance where a process running at high privilege loads a binary that is ACL'd to allow low privilege user tampering. Here are a few examples of those detections:
useful detection rules for both scenarios. First, the Veramine sensor provides deep visibility into the operation of Windows services
several very useful kinds of detection for this scenario. First, our rules-based detection pipeline highlights any
detects instances where an application has changed the accessibility features in a manner that looks like the "Sticky Keys" style attack. Here is an example detection: