Launch a password spray / brute force attach via Amazon AWS passthrough proxies, shifting the requesting IP address for every authentication attempt. This dynamically creates FireProx APIs for more evasive password sprays.
Shoutout to @ustayready for his CredKing and FireProx tools, which form the base of this suite.
See all the full notes on the Wiki, tool released with specifics in this blogpost
For detection tips, see the blogpost and detection section.
Be careful for account lockouts, know the reset policies of your target
- Rotates the requesting IP address for every request
- Automatically generates APIs for proxy passthru
- Spoofs API tracking numbers, forwarded-for IPs, and other proxy tracking headers
- Multi-threaded processing
- Password delay counters & configuration for lockout policy evasion
- Easily add new plugins
- WeekdayWarrior setting for timed spraying and SOC evasion
- Fully anonymous
The following plugins are currently supported:
- OWA - Outlook Web Access
- EWS - Exchange Web Services
- O365 - Office365
- O365Enum - Office365 User Enum (No Authentication Request)
- MSOL - Microsoft Online
- Okta - Okta Authentication Portal
- FortinetVPN - Fortinet VPN Client
- HTTPBrute - Generic HTTP Brute Methods (Basic/Digest/NTLM)
- ADFS - Active Directory Federation Services
- AzureSSO - Azure AD Seamless SSO Endpoint
- GmailEnum - Gmail User Enumeration (No Authentication Request)
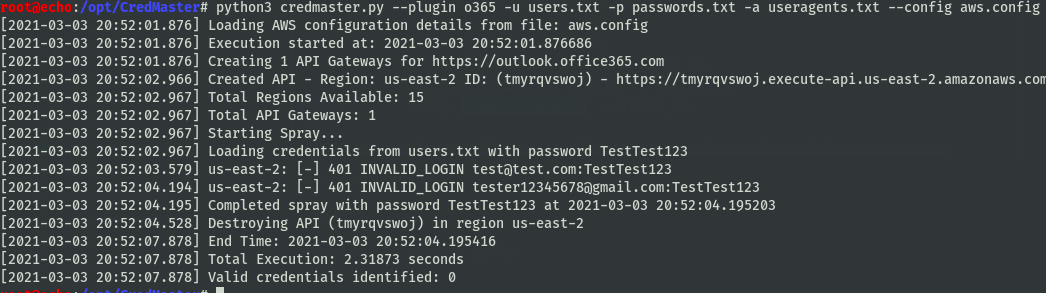
Example Use:
python3 credmaster.py --plugin {pluginname} --access_key {key} --secret_access_key {key} -u userfile -p passwordfile -a useragentfile {otherargs}
This tool requires AWS API access keys, a walkthrough on how to acquire these keys can be found here: https://bond-o.medium.com/aws-pass-through-proxy-84f1f7fa4b4b
All other usage details can be found here
PRs welcome :)
- New Plugin: Optiv's Go365 Method - Includes Office365 auth and userenum capabilities via SOAP
- "Resume" functionality for paused/cancelled scans. Ideally storing data for APIs used, if they were destroyed and what user/pwd the spray was on
- Password file read dynamically so you can add/delete pwds mid-scan and it will perform as desired
- Method to reliably determine if an auth attempt was throttled, so the username could be re-queued and tried again later for full cover (would have to be per-plugin, return "throttled" boolean value in plugin script, requeue if throttled)
- Notification system for webhooks
- Automatic logging of valid users
- Stop on success flag
- Spray profile overhaul
- Config file overhaul
- Development notes
- Mike Felch (ustayready) - CredKing & FireProx
- Beau Bullock (dafthack) - MSOLSpray tool
- Martin Ingesen (mrtn9) - MSOLSpray Python tool
- Oliver Morton (grimhacker) - Office365UserEnum tool
- Marcello (byt3bl33d3r) - SprayingToolkit
- Erforschr - HTTP Bruteforce tool
- Florian Hauser (frycos from codewhitesec) - ADFS plugin
- nyxgeek - Azure AD Seamless SSO python implementation
- Joe Helle (joehelle) - Oh365UserFinder
- Cameron Geehr (BarrelTit0r) - o365enum tool
- Max Gruenberg (Max_Gruenberg) - o365enum plugin
- x0rz - GmailEnum technique
- Kole Swesey (0xPanic_) - Assorted PR
- Logan (TheToddLuci0) - Assorted PRs
Feel free to drop me a line
- @knave on Keybase
- Twitter - knavesec