1Panel open source panel project has an unauthorized vulnerability.
Package
Affected versions
<= 1.10.0-lts
Patched versions
1.10.1-lts
Description
Published to the GitHub Advisory Database
Mar 6, 2024
Reviewed
Mar 6, 2024
Published by the National Vulnerability Database
Mar 6, 2024
Last updated
Mar 24, 2024
Impact
The steps are as follows:
Access https://IP:PORT/ in the browser, which prompts the user to access with a secure entry point.

Use Burp to intercept:
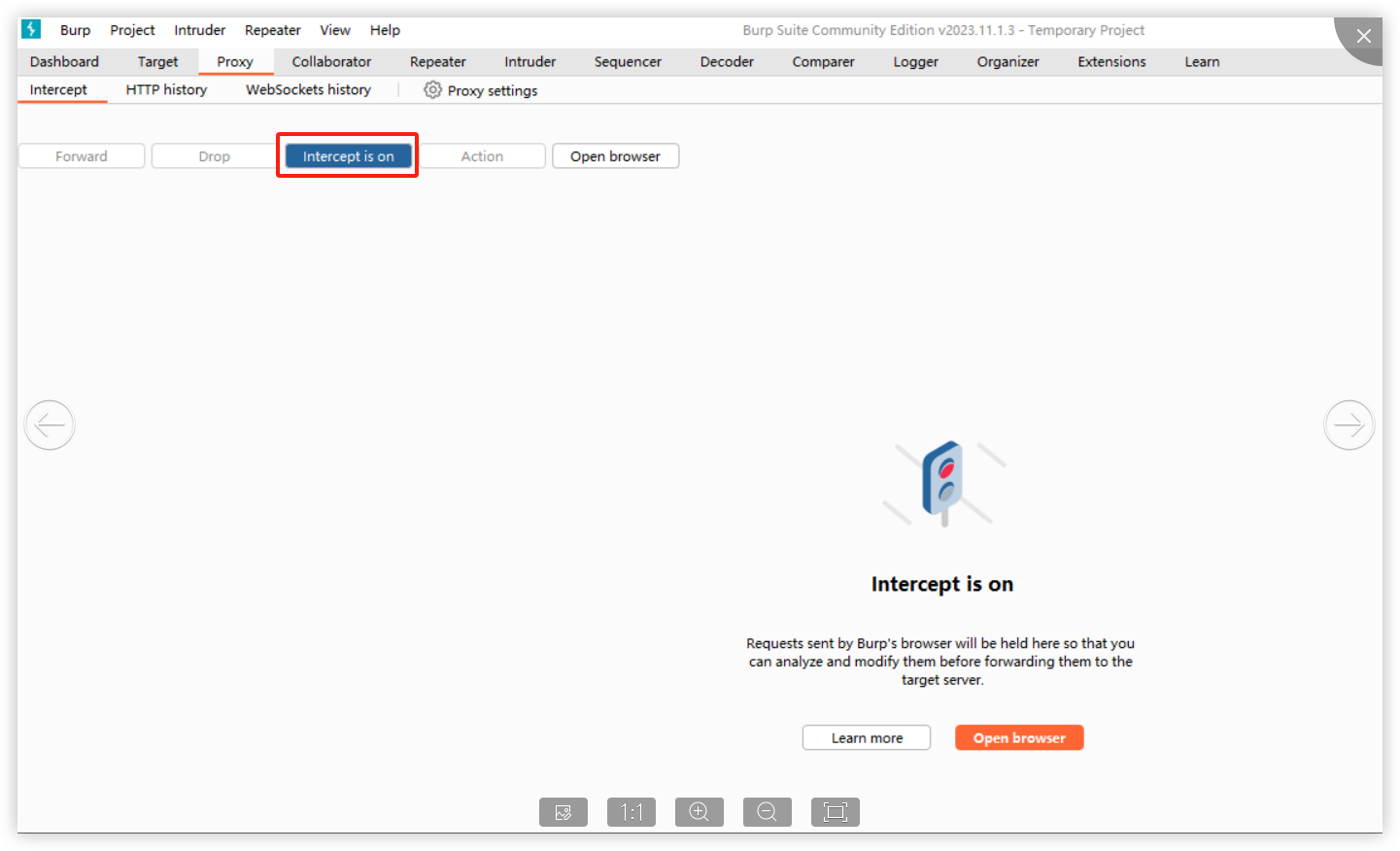
When opening the browser and entering the URL (allowing the first intercepted packet through Burp), the following is displayed:
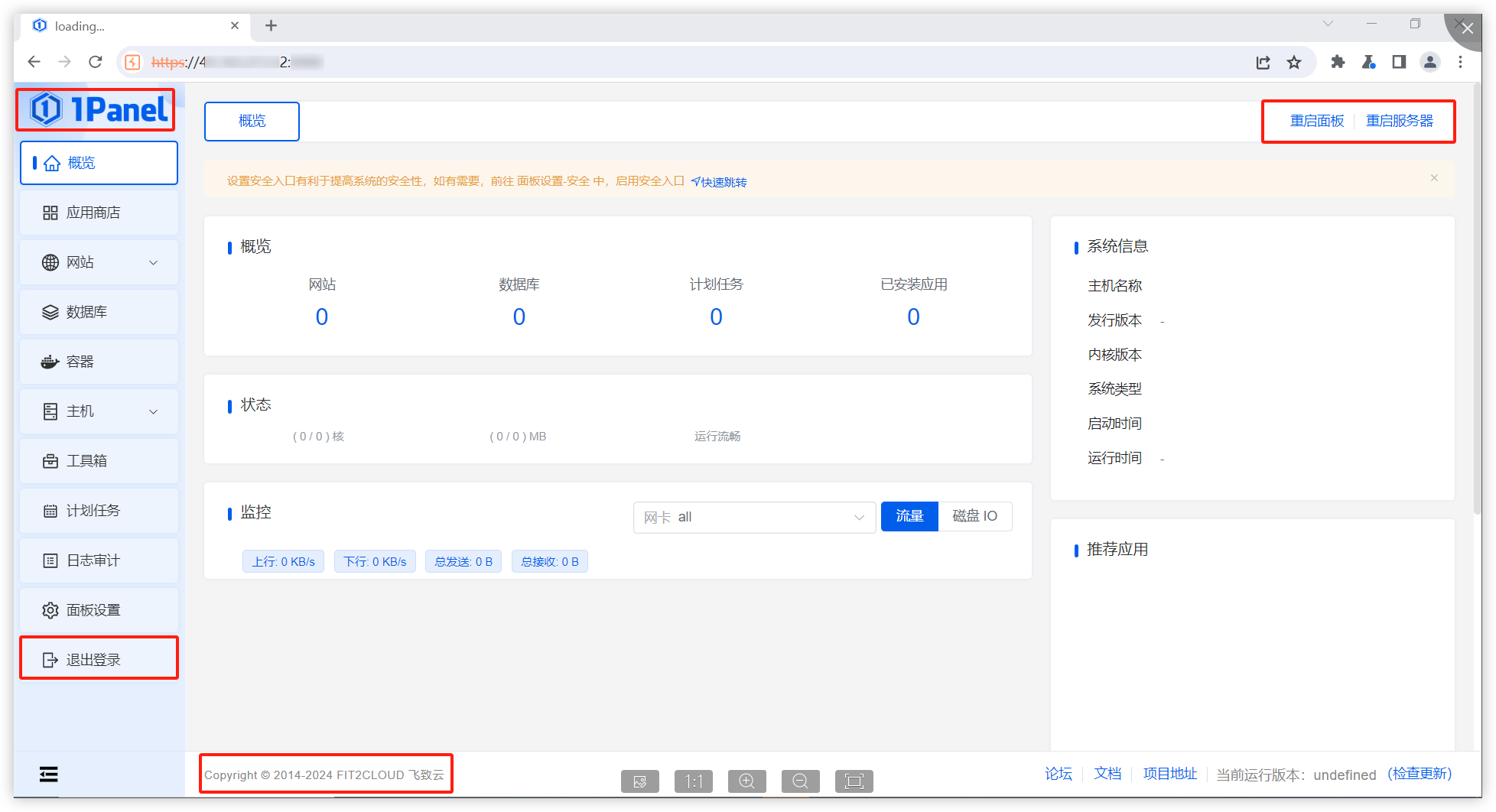
It is found that in this situation, we can access the console page (although no data is returned and no modification operations can be performed)."
Affected versions: <= 1.10.0-lts
Patches
The vulnerability has been fixed in v1.10.1-lts.
Workarounds
It is recommended to upgrade the version to 1.10.1-lts.
References
If you have any questions or comments about this advisory:
Open an issue in https://github.com/1Panel-dev/1Panel
Email us at [email protected]
References